
Welcome {{ first name | reader }} to a 🔒 pro subscriber-only deep dive 🔒.
Brought to you by:
👣 Smallstep – Secures Wi-Fi, VPNs, ZTNA, SaaS and APIs with hardware-bound credentials powered by ACME Device Attestation
📊 LockThreat – AI-powered GRC that replaces legacy tools and unifies compliance, risk, audit and vendor management in one platform
Forwarded this email? Join 70,000 weekly readers by signing up now.
#OpenToWork? Try our AI Resume Builder to boost your chances of getting hired!
—
Get lifetime access to our deep dives, weekly cyber intel podcast report, premium content, AI Resume Builder, and more — all for just $799. Corporate plans are now available too.
Executive Summary
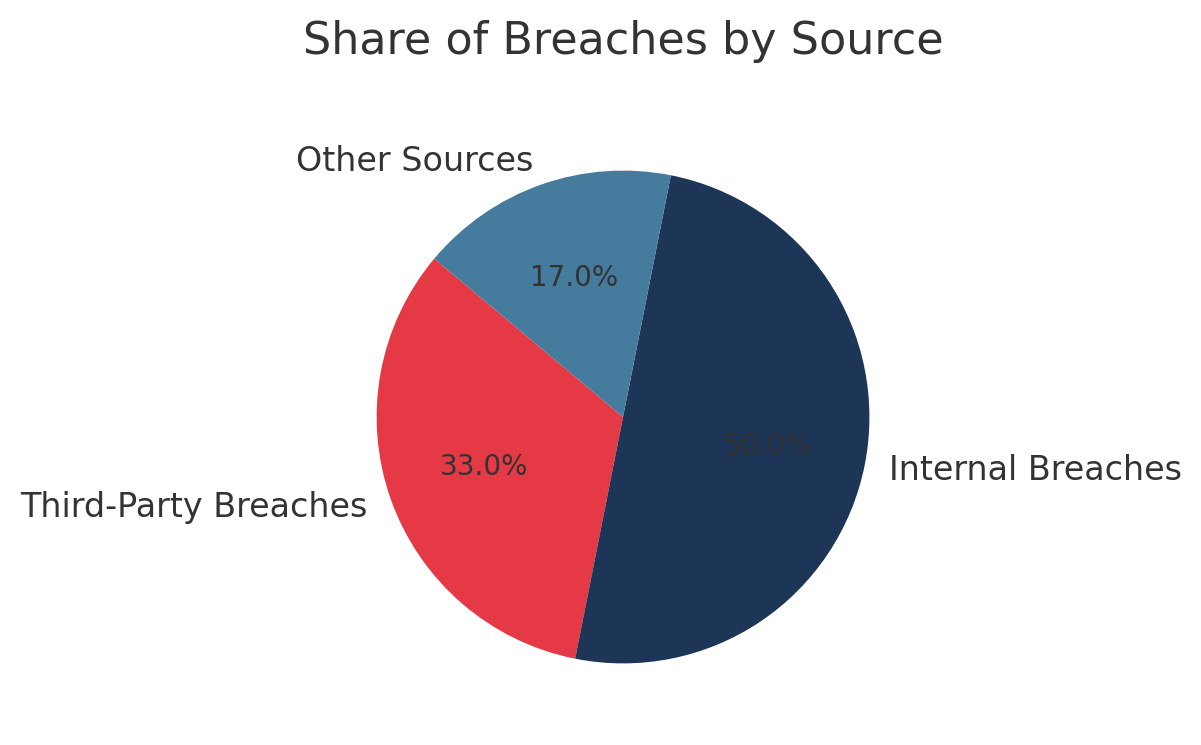
Vendor disengagement has emerged from administrative obscurity to become a critical cybersecurity imperative. Analysis of 47 recent data breaches reveals that third-party incidents now account for 33% of all breaches, with supply chain attacks surging 236% over the past two years. Yet 59% of organizations fail to actively assess third-party risks during offboarding, creating a dangerous gap in their security posture.
This whitepaper, drawing from 23 industry frameworks including NIST CSF 2.0, ISO 27001:2022, and SOC 2 requirements, provides CISOs with a comprehensive roadmap for building vendor disengagement playbooks. Recent enforcement actions underscore the urgency: AT&T faced $13 million in fines after a former cloud vendor retained customer data years post-termination, while Morgan Stanley paid $155 million for inadequate oversight of vendor data destruction.
The research identifies five critical success factors: CEO-level governance oversight (correlating with 40% higher EBIT impact from third-party risk management), fundamental workflow redesign during vendor transitions, automated access revocation within 24-48 hours of termination, risk-tiered offboarding protocols, and continuous post-termination monitoring for 90 days minimum.
Organizations with revenues exceeding $500 million are implementing these practices at twice the rate of smaller companies, creating a maturity gap that threatens competitive positioning. For CISOs, building robust vendor disengagement playbooks is no longer optional - it is a fundamental business necessity that reduces data breach risk by up to 50% in high-tier vendor scenarios while ensuring regulatory compliance with GDPR, DORA, and emerging frameworks like NIS2.
Subscribe to CybersecurityHQ Newsletter to unlock the rest.
Become a paying subscriber of CybersecurityHQ Newsletter to get access to this post and other subscriber-only content.
Upgrade to paidA subscription gets you:
- Access to Deep Dives and Premium Content
- Access to AI Resume Builder
- Access to the Archives

