Welcome {{ first name | reader }} to a 🔒 pro subscriber-only deep dive 🔒.
Brought to you by:
👣 Smallstep – Secures Wi-Fi, VPNs, ZTNA, SaaS and APIs with hardware-bound credentials powered by ACME Device Attestation
📊 LockThreat – AI-powered GRC that replaces legacy tools and unifies compliance, risk, audit and vendor management in one platform
Forwarded this email? Join 70,000 weekly readers by signing up now.
#OpenToWork? Try our AI Resume Builder to boost your chances of getting hired!
—
Get lifetime access to our deep dives, weekly cyber intel podcast report, premium content, AI Resume Builder, and more — all for just $799. Corporate plans are now available too.
Executive Summary
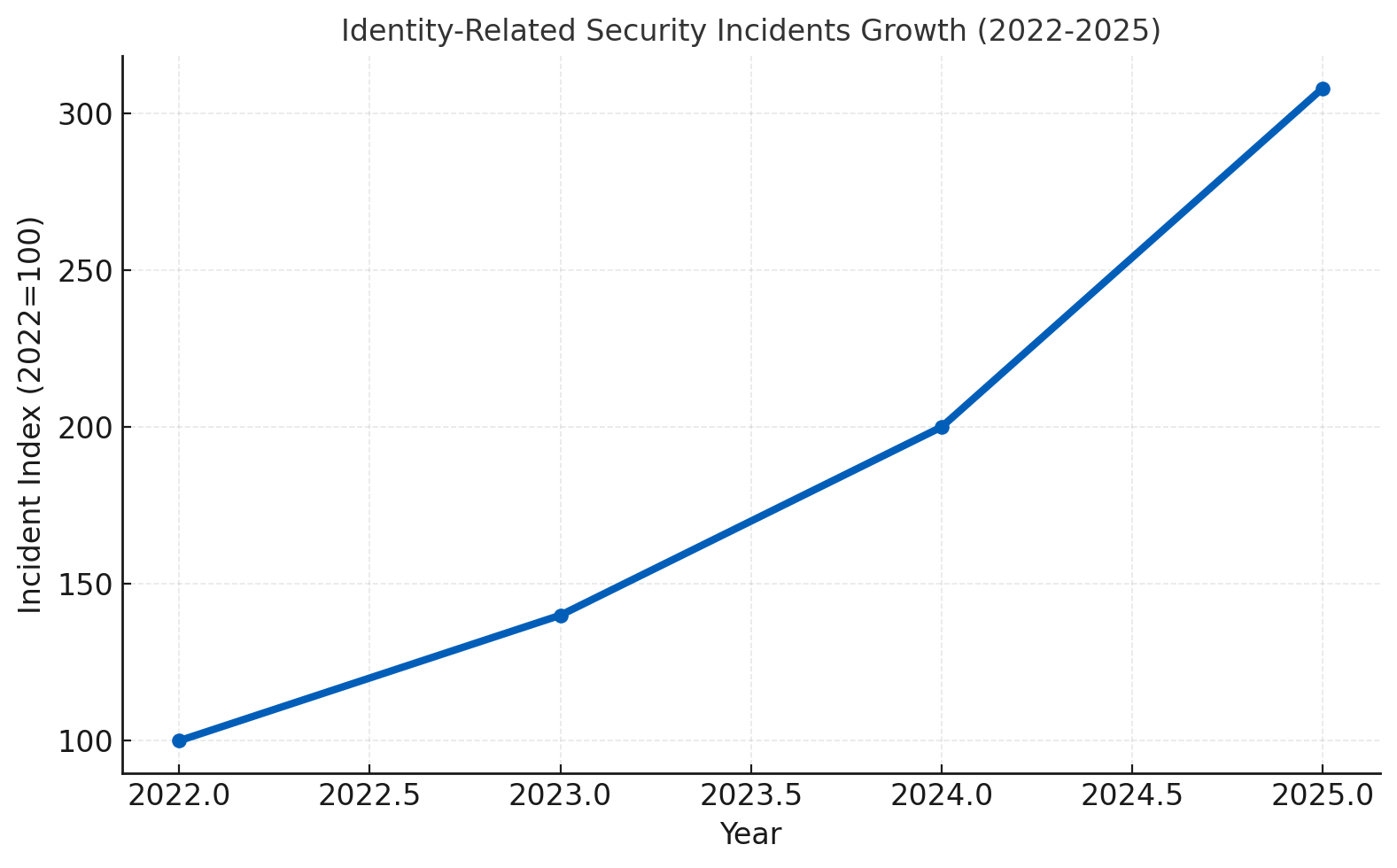
The enterprise security landscape stands at a critical inflection point. Analysis of the 2025 Verizon Data Breach Investigations Report reveals that stolen credentials remain the leading initial access method, while identity-related incidents increased 54% year-over-year, with 85% attributed to compromised machine identities. The Model Context Protocol (MCP) - introduced by Anthropic in late 2024 - is rapidly emerging as the standard interface for AI-driven automation, creating autonomous agents that will inherit and amplify every weakness in today's fractured identity infrastructure.
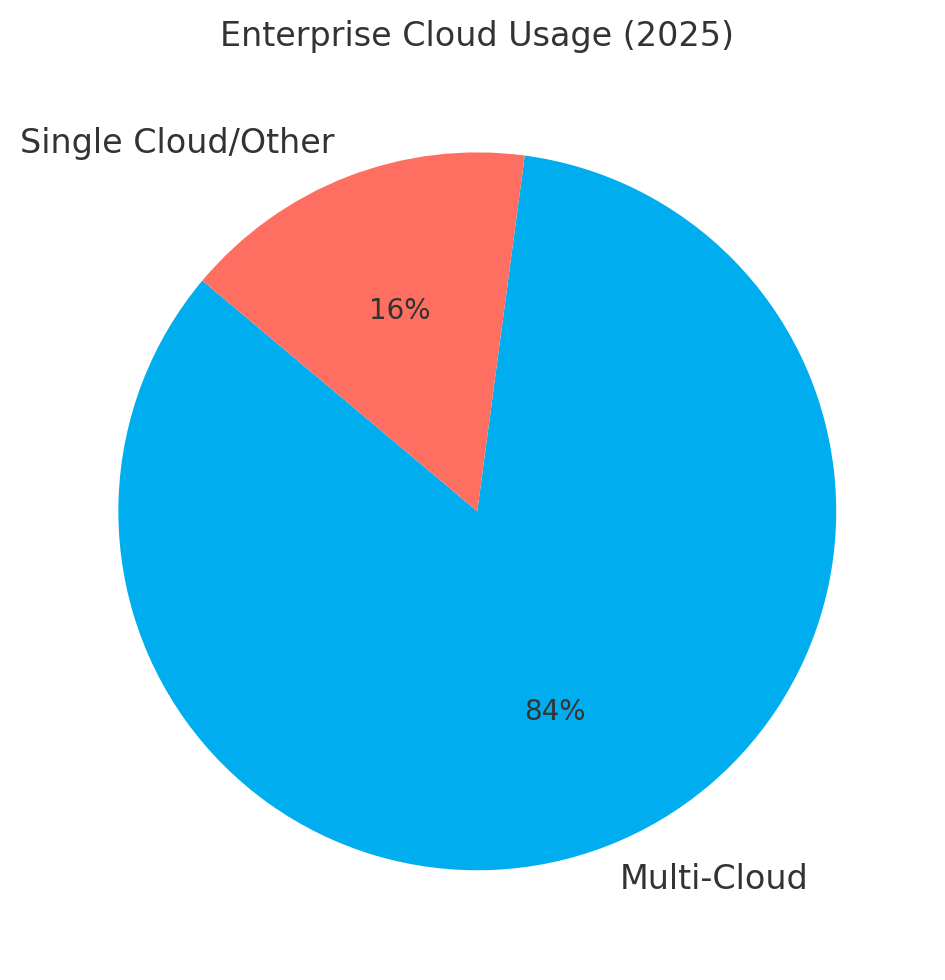
Organizations face compound risk: 84% operate across multiple cloud platforms with siloed identity systems, while 71% have deployed generative AI in at least one business function. AI agents operating via MCP can chain together disparate permissions at machine speed, turning individually low-risk access rights into high-risk data exfiltration pathways that static security tools cannot detect.
The financial stakes are substantial. While the global average cost of a data breach is $4.44 million, multi-cloud breaches average $5.05 million, and credential-based breaches average $4.92 million. Third-party breaches have doubled year-over-year, now accounting for 30% of incidents - a trend that will accelerate as organizations deploy autonomous AI agents traversing organizational boundaries.
This whitepaper introduces a Multi-Dimensional Trust Framework specifically architected for MCP-driven workflows. Unlike traditional models establishing trust once at authentication, this framework treats trust as a continuously calculated composite score from four pillars: Agent Attestation, Tool and Server Verification, Contextual Validation, and Data Sensitivity. The framework defines four actionable trust levels - Constrained, Verified, Adaptive, and Zero-Knowledge - each with specific technical requirements.
Organizations that fundamentally redesign workflows as they deploy AI report measurably higher bottom-line impact. Yet only 21% have taken this critical step. The roadmap presented here provides CISOs with a phased, 24-month implementation plan spanning foundation building, pilot deployment, organizational scaling, and continuous optimization.
Subscribe to CybersecurityHQ Newsletter to unlock the rest.
Become a paying subscriber of CybersecurityHQ Newsletter to get access to this post and other subscriber-only content.
Upgrade to paidA subscription gets you:
- Access to Deep Dives and Premium Content
- Access to AI Resume Builder
- Access to the Archives

