
Welcome {{ first name | reader }} to a 🔒 pro subscriber-only deep dive 🔒.
Brought to you by:
👣 Smallstep – Secures Wi-Fi, VPNs, ZTNA, SaaS and APIs with hardware-bound credentials powered by ACME Device Attestation
📊 LockThreat – AI-powered GRC that replaces legacy tools and unifies compliance, risk, audit and vendor management in one platform
Forwarded this email? Join 70,000 weekly readers by signing up now.
#OpenToWork? Try our AI Resume Builder to boost your chances of getting hired!
—
Get lifetime access to our deep dives, weekly cyber intel podcast report, premium content, AI Resume Builder, and more — all for just $799. Corporate plans are now available too.
Executive Summary
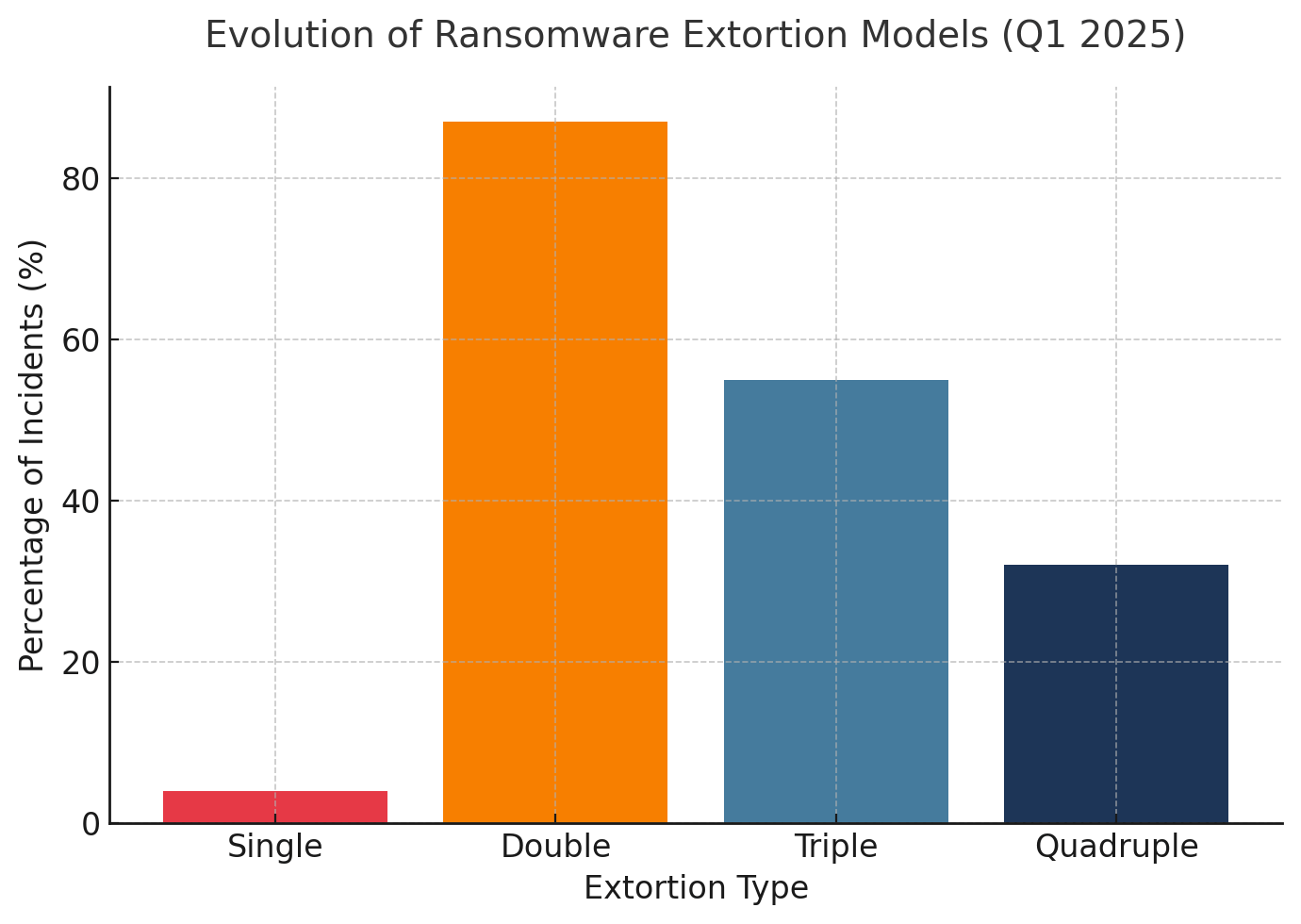
Based on analysis of 1,497 ransomware incidents in Q1 2025 and examination of 96% of cases involving data exfiltration, the ransomware landscape has fundamentally transformed from simple encryption attacks to sophisticated multi-layered extortion campaigns. Drawing from 23 industry frameworks and regulatory responses across 45 nations, this whitepaper reveals that while double extortion remains the baseline in 87-96% of attacks, triple and quadruple extortion tactics are rapidly becoming normalized, with organizations facing average recovery costs of $1.53 million and median ransom payments jumping from $200,000 in 2023 to $1.5 million in 2024.
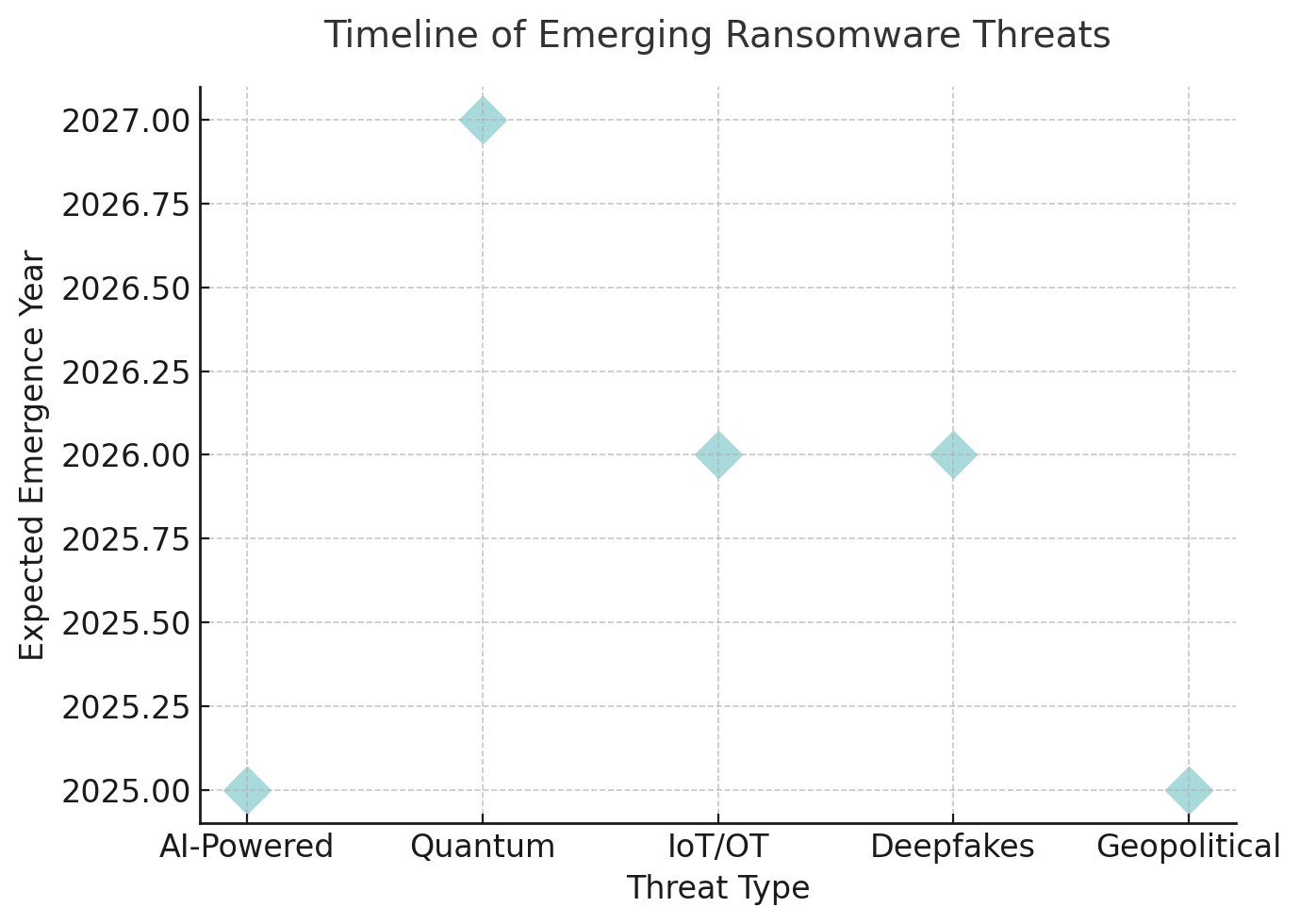
The evolution from single to quadruple extortion represents a calculated response by threat actors to improved organizational defenses. As 49.5% of victims successfully restore from backups - a 360% increase from 2022 - attackers have systematically added pressure points: data theft and leak threats (double extortion), distributed denial-of-service attacks (triple extortion), and direct harassment of customers, partners, and stakeholders (quadruple extortion). This multi-front siege transforms ransomware from an IT incident into a full-spectrum business crisis affecting operational continuity, regulatory compliance, brand reputation, and stakeholder trust.
For Chief Information Security Officers navigating this threat landscape in 2025, the strategic imperatives are clear: ransomware defense requires enterprise-wide transformation, not just technical controls. Organizations implementing comprehensive multi-extortion resilience strategies - including CEO-level governance, workflow redesign, proactive threat intelligence, and ecosystem-wide incident response capabilities - report 44% lower recovery costs and 50% reduction in initial access success rates. The window for action is narrowing as median dwell times compress to just 4 days and breakout times average 48 minutes, demanding real-time detection and orchestrated response capabilities that span technology, process, and people dimensions.
Subscribe to CybersecurityHQ Newsletter to unlock the rest.
Become a paying subscriber of CybersecurityHQ Newsletter to get access to this post and other subscriber-only content.
Upgrade to paidA subscription gets you:
- Access to Deep Dives and Premium Content
- Access to AI Resume Builder
- Access to the Archives

